Elisity Unveils Zero Trust Access for Hybrid Clouds

Elisity Inc., a San Jose, Calif.-based startup, has emerged from stealth, claiming a solution that combines zero-trust networking with software-defined perimeters. Called Elisity Cognitive Trust (ECT), the flagship creates a virtual fabric, or “e-mesh,” based on a network’s IP/MPLS infrastructure, which secures communications between users and all cloud or premises-based resources, local or remote.
The concept of separating security from underlying hardware and software isn’t new. The approach is universally espoused, at least in theory, by router, switch, and firewall vendors. And it is the basis for a range of cloud-oriented security solutions, such as those from Aporeto, the startup bought by Palo Alto Networks (PANW) late in 2019, or Zscaler (ZS), which similarly touts cloud-based services that control remote access to private clouds and the Internet.
But Elisity says ECT is different because it covers not only applications and users but also Internet of Things (IoT) devices and data center hardware. Through its virtualized fabric, ECT secures private clouds, data center networks, public cloud services, and permutations and combinations of all these environments (see diagram below). It integrates with major cloud providers (AWS, Microsoft Azure, Google Cloud Platform, etc.) and with other products, such as data analytics from Splunk Inc. (SPLK).
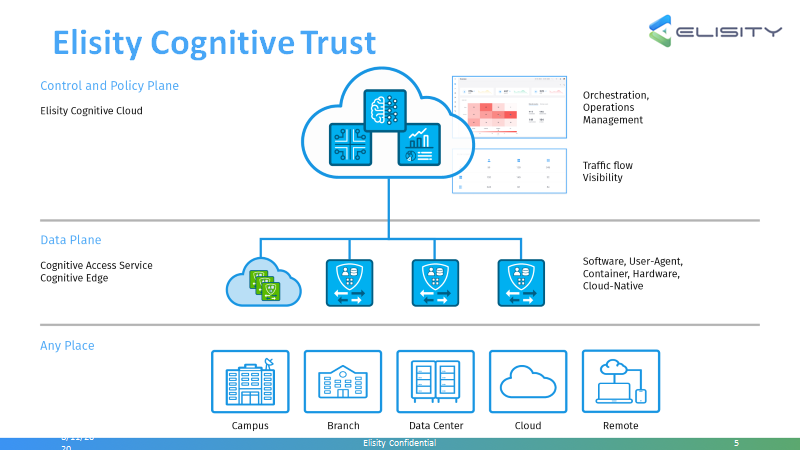
Source: Elisity Inc.
Addressing the Larger Cloud Attack Surface
ECT governs access to all these elements through policies informed by an artificial intelligence (AI) engine. This software monitors all connections for anomalies and recommends policy changes based on its findings.
Elisity’s solution is meant to span the proliferation of data sources and locations in today’s increasingly polyglot networks — a bigger attack surface than ever. “As a result of digital transformation efforts, most enterprises will have more applications, services, and data outside their enterprises than inside. ECT places the security controls where the users and applications are — in the cloud,” said Sundher Narayan, co-founder and chief architect at Elisity, in a statement.
As noted, there’s plenty of competition in this space. Besides the networking hardware suppliers, cybersecurity players, and analytics vendors, there also are managed service providers, such as Sentinel Technologies, which offers security information and event management (SIEM) solutions as a service.